Stop Managing Penetration Test Findings in Spreadsheets and Losing €3,600 Quarterly in Missed Retests
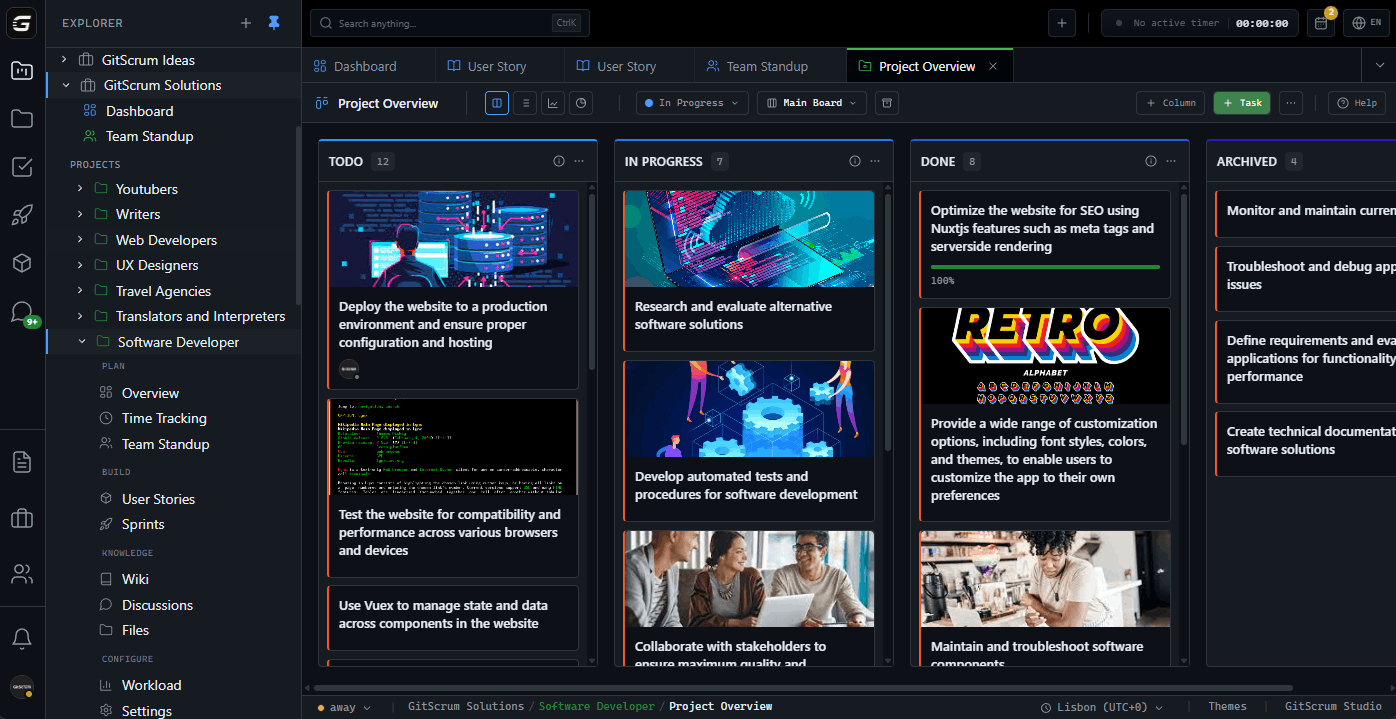
If you're the principal consultant or managing partner at a cybersecurity consultancy with 5-20 people, you know the chaos: findings documented in Word docs and Excel. Client says they fixed CVE-2024-XXXX—but you can't find your original notes. Retest opportunities slip by because nobody tracks remediation status. Client asks for evidence of what you reported 6 months ago—you spend 3 hours reconstructing the audit trail. You've looked at Dradis, PlexTrac, AttackForge—but €800/month for 'pentest management' when you just need organized findings is excessive. You need one place where every finding, every communication, and every retest lives—with proper client isolation.
problem.identify()
The Real Cost of Spreadsheet-Based Finding Management
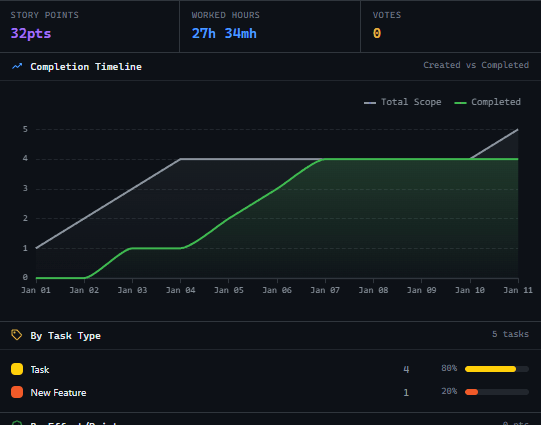
Missed Retest Revenue = €3,600/Quarter in Lost Billable Engagements
Client fixed 12 critical findings. Asked for retest. It's in an email somewhere. Nobody tracked it. 3 months later, client hired another firm for the retest because you never followed up. 6 missed retests/year × €2,400 average retest engagement = €14,400 in lost revenue because 'retest needed' lived in email, not a tracked status.
Finding Archaeology = €4,800/Year in Non-Billable Reconstruction
Client dispute: 'You never told us about that SQL injection.' Your principal consultant spends 4 hours reconstructing evidence from Word docs, Excel sheets, and email threads to prove timeline. Happens 8 times/year. 8 × 4 hours × €150/hour (principal rate) = €4,800 in non-billable evidence reconstruction.
Client Data Mixing = €12,000 in Potential Liability
Junior consultant accidentally includes Client A's network diagram in Client B's report. You catch it before delivery—this time. Near-miss happens 4 times/year. One actual breach disclosure could mean regulatory fines, lawsuit, and reputation damage. Conservative liability exposure: €12,000+ per incident if it reaches the client.
Severity Tracking Chaos = €2,400/Year in Misallocated Effort
Team works on medium-severity findings while critical findings wait because severity wasn't consistently tracked. Client asks 'what's the status of the criticals?'—you don't know without opening 15 files. Result: 2 hours/week spent on prioritization meetings that shouldn't exist. 2h × 50 weeks × €24/hour = €2,400 in unnecessary coordination.
Sound familiar?
See how GitScrum handles this in 2 minutes.
solution.implement()
Every Finding Tracked, Every Retest Scheduled, Every Client Isolated
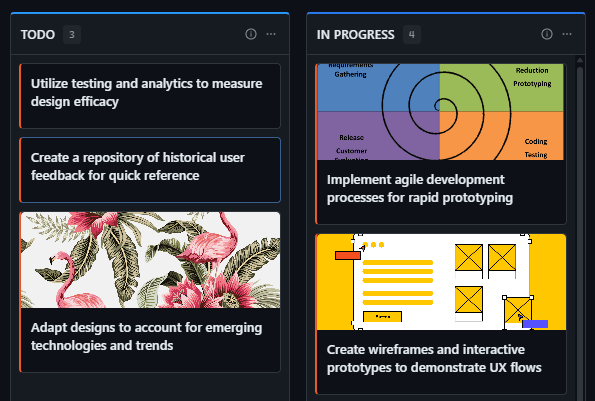
Finding → Card with Severity, Evidence, Remediation Status
Every finding becomes a tracked card. Attach screenshots, logs, CVE references. Tag severity: Critical, High, Medium, Low. Track status: Open, In Remediation, Ready for Retest, Verified Closed. Filter all findings across all clients by severity—know every critical that's still open in 30 seconds.
Strict Client Isolation = Zero Cross-Contamination Risk
Each client gets isolated workspace. Consultants see only clients they're assigned to. Methodologies and templates live in shared library, but client data never mixes. Accidentally include Client A data in Client B report? Impossible—you can't access both simultaneously.
Automatic Retest Tracking = Zero Missed Revenue
Client marks finding as remediated? Card moves to 'Ready for Retest' automatically. Dashboard shows all pending retests across all clients. Weekly notification: '8 retests awaiting scheduling.' Never lose retest revenue because it was buried in email again.
Timestamped Evidence Trail = Instant Dispute Resolution
Every finding has full audit trail: when created, what was attached, when communicated to client, client acknowledgment. Dispute about timeline? Pull up the card. Timestamped evidence resolves it in 2 minutes instead of 4 hours of reconstruction.

These solutions work together. Try them today.
Team size GitScrum is built for
For teams up to 2 users
Per user, per month
"We stopped losing hours to status meetings. Now everyone sees progress in real-time."
Sarah Chen
Operations Lead, 15-person team
Frequently Asked Questions
Still have questions? Contact us at customer.service@gitscrum.com
We need SOC 2 compliant platforms. Is this?
GitScrum is not SOC 2 Type II certified. If your contracts require certified platforms with formal attestations—use Dradis, PlexTrac, or enterprise GRC tools. GitScrum is for consultancies whose clients care about security posture improvement, not vendor compliance certification.
Can we import findings from Nessus/Burp/other scanners?
No automated scanner integration. You create finding cards manually or via our API. If you need automated import from 15 different scanners—that's €800/month tools territory. GitScrum is for organizing human-generated findings and tracking remediation, not replacing scanner import pipelines.
Can clients see their findings and mark remediation?
Yes. Give clients portal access to their workspace only. They see their findings, can mark as 'remediated,' and request retests. They cannot see other clients or your internal consultant notes. You control what's visible.
What about findings that need NDA clearance before sharing details?
Create finding with restricted visibility—client sees it exists but content is gated until you release it. Useful for responsible disclosure timelines or legal-sensitive findings.
Ready to solve this?
Start free, no credit card required. Cancel anytime.










