Stop Losing €38,000/Year in Audit Failures and Compliance Rework
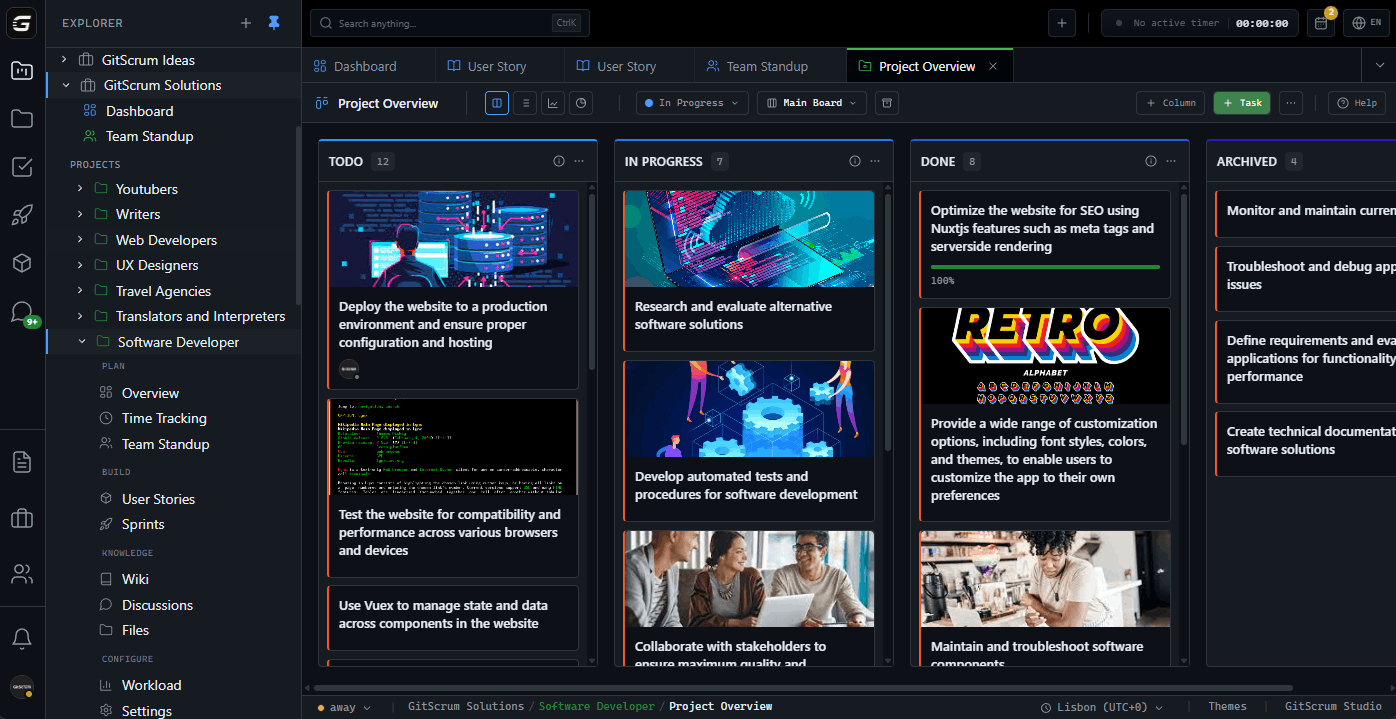
If you're the CTO or engineering lead at a FinTech company with 5-20 people, your auditor just asked who approved the last database schema change. Nobody documented it. Your SOC 2 certification is at risk because your change management 'process' lives in Slack threads nobody can find. 13-person FinTech teams using GitScrum reduced audit prep from 6 weeks of scrambling to 3 days of exports.
problem.identify()
The Hidden Cost of 'Good Enough' Compliance
Audit Prep Becomes Engineering Freeze
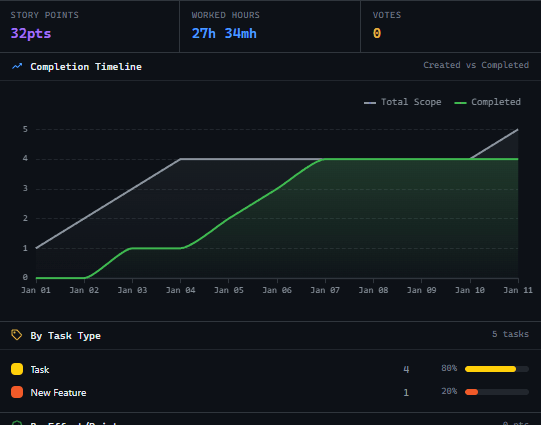
2-3 engineers × 6 weeks of audit documentation scramble × €80/hour = €28,800/year in engineering time lost. Plus the 4-6 weeks of delayed features while your best engineers reconstruct approvals from memory and Slack archaeology.
Security Review Bottlenecks Block Releases
Payment features sit waiting for security sign-off nobody scheduled. 2-3 week delays per quarter × €2,500 average delay cost per feature = €10,000/year. Your competitors ship while you wait for informal approval chains to clear.
Post-Facto Documentation Fiction
Code ships, then months later compliance asks for design docs. Engineers spend 3-4 hours per feature reconstructing decisions they barely remember. 20 features/year × 3.5 hours × €80/hour = €5,600/year writing documentation fiction.
Regulatory Change Panic
New PCI requirements announced. 90 days to comply. 2 engineers × 3 weeks emergency impact assessment + remediation planning = €9,600/year. Because nobody documented which systems process card data, you're re-discovering your own architecture under deadline.
Sound familiar?
See how GitScrum handles this in 2 minutes.
solution.implement()
How PaymentFlow Labs Eliminated €38,000/Year in Compliance Overhead
Automatic Audit Trail Generation
Every change automatically logs who requested, who reviewed, who approved, and when—in a format auditors actually want. Export SOC 2 evidence in 3 clicks instead of 6 weeks of Slack archaeology.
Security Review Workflow Integration
Payment features automatically queue for security review. Security team sees their backlog. Features can't move to production until security signs off in the system. No more informal approvals lost in DMs.
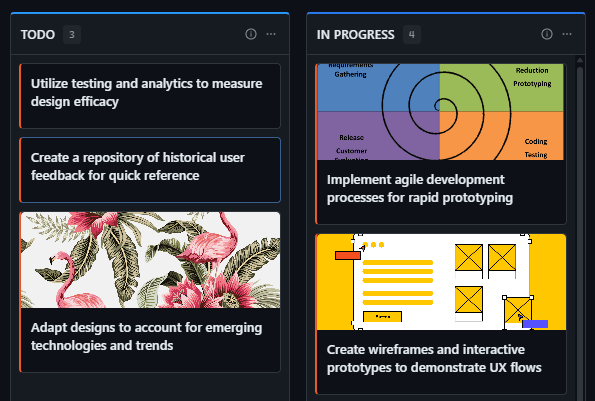
Living Compliance Documentation
Document architecture decisions and compliance implications as features are built. Documentation linked to actual code changes. When auditors ask about a feature, show them the trail from decision to deployment.
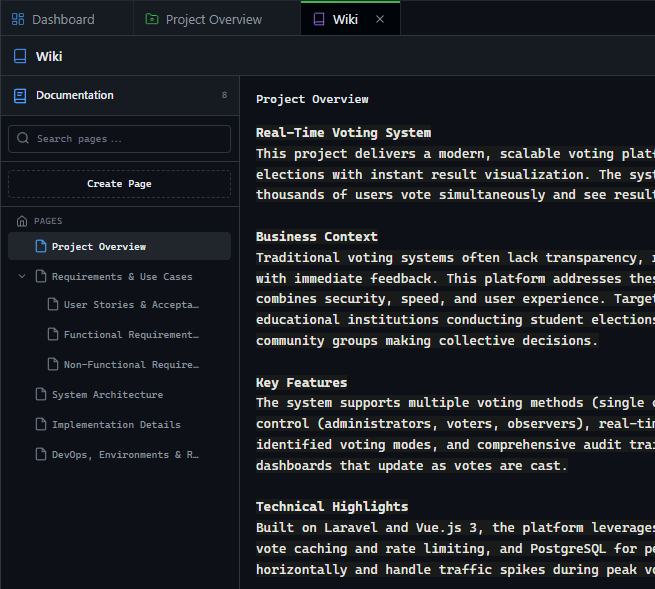
Regulatory Impact Mapping
Tag systems with compliance scope (PCI, SOC 2, GDPR). When new regulations hit, filter to see exactly which systems are affected. Generate impact assessments in hours instead of weeks of discovery.
These solutions work together. Try them today.
Team size GitScrum is built for
For teams up to 2 users
Per user, per month
"We stopped losing hours to status meetings. Now everyone sees progress in real-time."
Sarah Chen
Operations Lead, 15-person team
Frequently Asked Questions
Still have questions? Contact us at customer.service@gitscrum.com
How does this integrate with our existing SOC 2 controls?
Map GitScrum workflows directly to your SOC 2 control matrix. Change request boards satisfy change management controls (CC6.1). Approval tracking satisfies access controls. Export evidence reports in formats auditors expect—no reformatting needed.
Can we restrict who can approve production changes involving payment data?
Yes. Role-based permissions ensure only authorized personnel can approve specific change types. Configure separate approval requirements for dev, staging, and production. Payment-touching changes can require senior engineer + security sign-off before deployment.
What about emergency production hotfixes at 2am?
Create expedited change workflows for emergencies. Deploy first, document during. Approvals can happen post-facto but must be logged within your defined window (24-48 hours typical). System tracks emergency changes separately for audit reporting with full context.
Ready to solve this?
Start free, no credit card required. Cancel anytime.










