The fragmented tool environment creates significant security risk during employee offboarding.
When someone leaves, IT must revoke access across every tool in the stack: GitHub (repository access), Jira (project visibility), Confluence (documentation), Slack (communication channels), cloud consoles (infrastructure), CI/CD systems (deployment pipelines), monitoring tools (system visibility), third-party integrations (API tokens). Each tool has a different deprovisioning process.
Some require admin console actions. Others need ticket submissions.
Some require command-line revocation. Personal API tokens may exist that are not tracked centrally.
OAuth connections may persist. The offboarding checklist attempts to track all this, but it is only as good as the current state of the tool stack—which changes constantly.
A tool added last month might not be on the checklist. A personal integration created by the departing employee might be unknown.
Audits regularly discover former employees with lingering access. A developer who left three months ago can still read the private GitHub repository.
A former contractor still has monitoring dashboard access. The security risk is real: data exfiltration, credential misuse, or simply embarrassment when a former employee accidentally posts to a still-connected Slack channel.
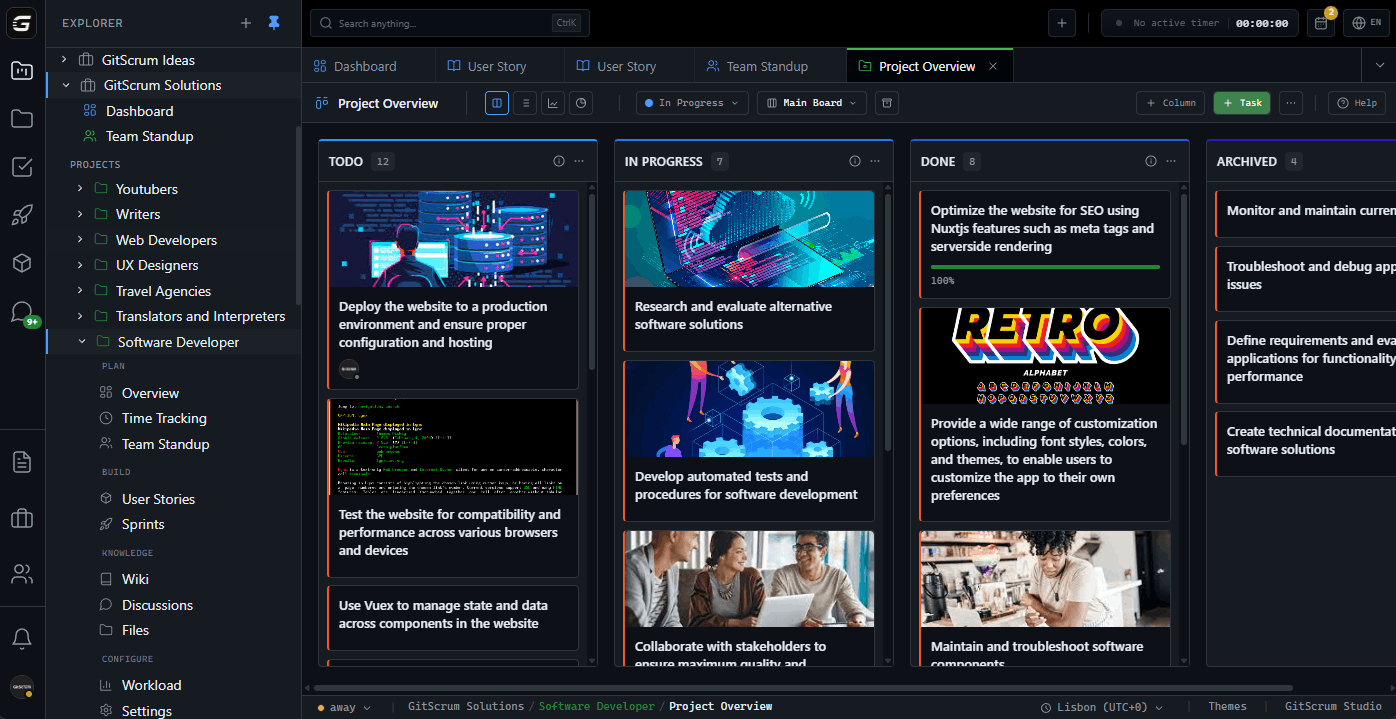
GitScrum's consolidated platform solves this with single-action offboarding. Deactivate the user account, and all access is revoked: tasks, documentation, communication, integrations—everything.
No scattered revocations to track. No tools to miss.
One action, complete security.
The GitScrum Advantage
One unified platform to eliminate context switching and recover productive hours.