The root problem isn't audits—it's that compliance evidence isn't collected as part of normal work.
Access is granted in Slack DMs that disappear. Code reviews happen but aren't systematically linked to requirements.
Change approvals exist somewhere in email threads. When the auditor asks for evidence, you're reconstructing history from fragments.
This reconstruction is expensive, error-prone, and stressful. And because it only happens before audits, nobody invests in better systems.
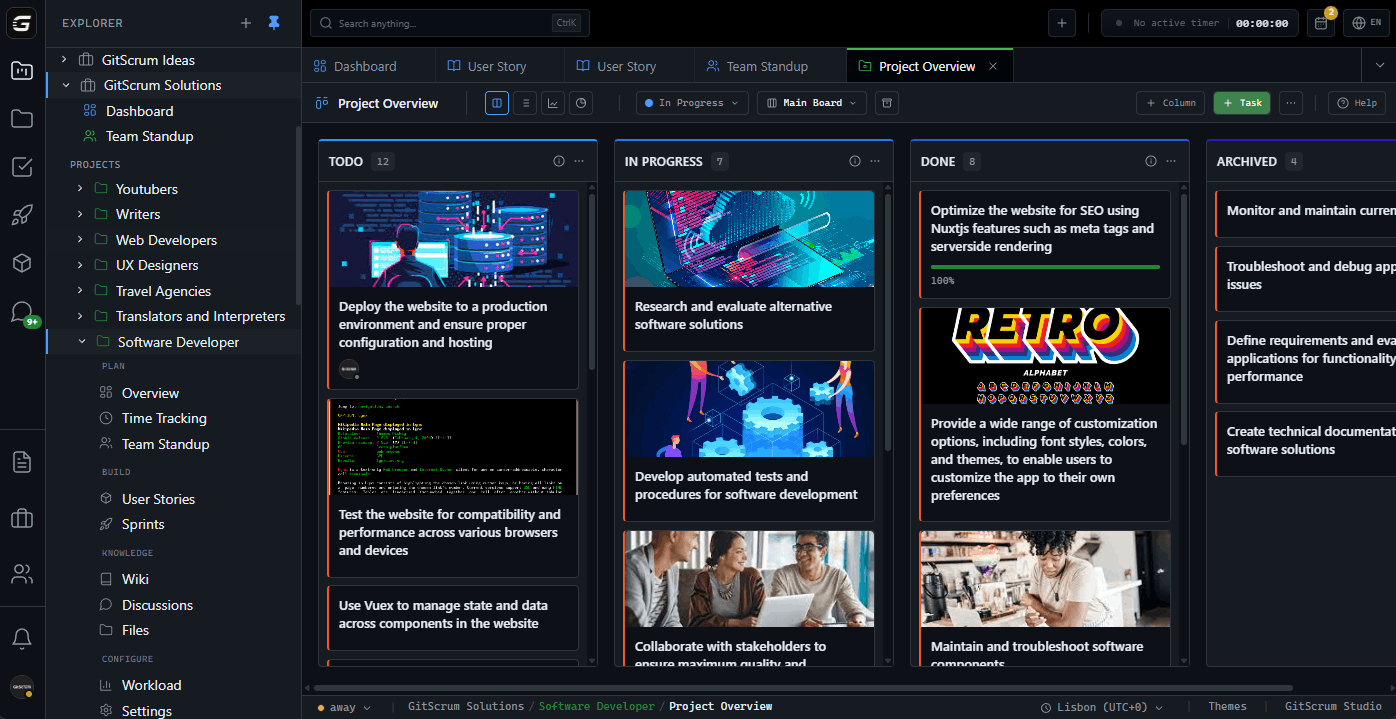
The GitScrum Advantage
One unified platform to eliminate context switching and recover productive hours.