Dependency management is a trap.
Stay current and you risk breaking changes with every update. Fall behind and you accumulate risk—security vulnerabilities, compatibility issues, and the eventual forced update that spans too many versions to debug.
Most teams oscillate between 'update everything' binges that cause outages and 'touch nothing' periods that accumulate risk. Neither approach is sustainable.
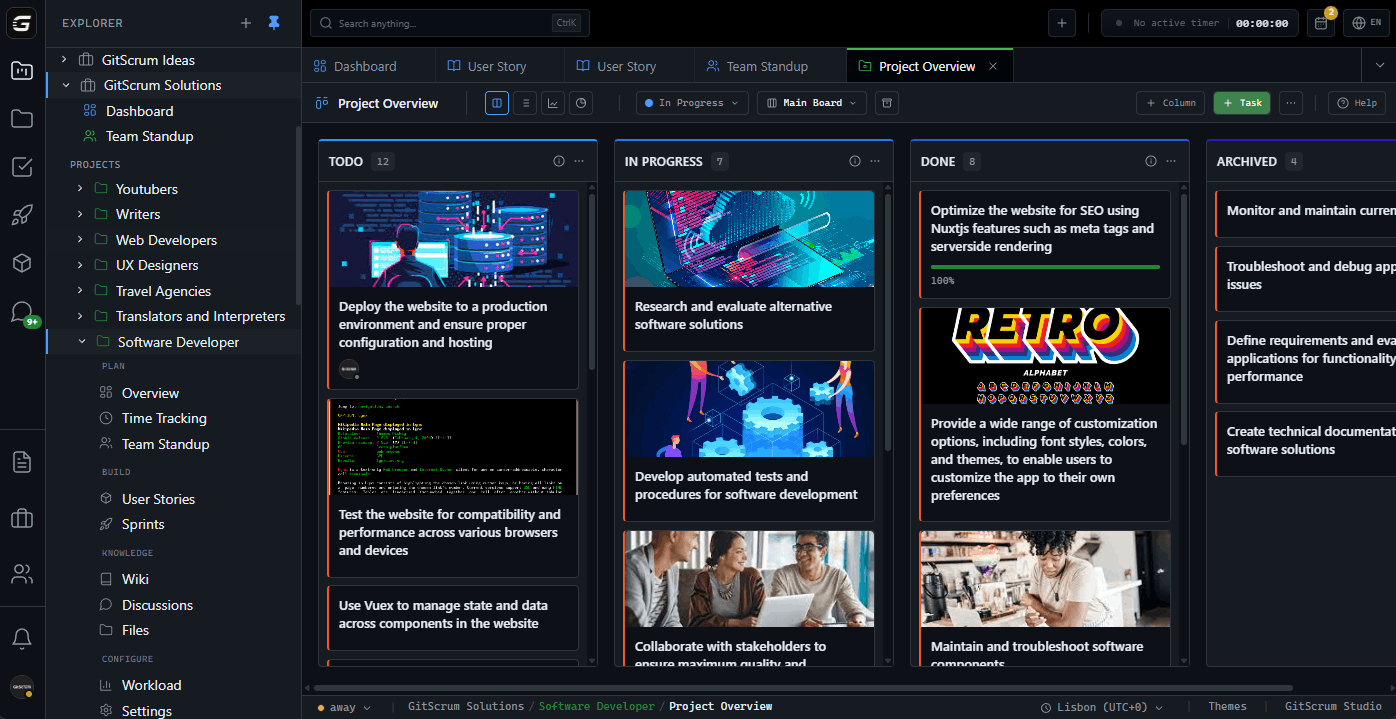
The GitScrum Advantage
One unified platform to eliminate context switching and recover productive hours.