The Fintech Development Challenge You're building financial software.
The stakes are different: - Regulatory compliance isn't optional - Security vulnerabilities can mean prison - Audit trails are legally required - Downtime costs millions per hour - Data handling has strict rules Yet your project management tool? Designed for generic software teams.
No compliance tracking. No audit logs.
No regulatory deadline management. The Compliance Documentation Problem Regulator asks: 'Show us the change history for the payment processing module.' Your current setup: - Code history: GitHub - Task decisions: Jira - Approval emails: Outlook - Meeting notes: Confluence - Compliance sign-offs: Spreadsheet Time to compile: 3-5 days Risk of missing something: High Auditor frustration: Maximum The Regulatory Deadline Problem PSD2 compliance deadline: March 15 PCI-DSS renewal: June 30 GDPR audit: September SOX requirements: Quarterly These aren't flexible.
Miss them = fines, license issues, or worse. But your sprint planning tool doesn't know about regulatory deadlines.
It just sees 'Story 1234 - Update payment flow.' The Security Review Bottleneck Every code change needs security review in fintech: - Pull request created - Waiting for security team... - Waiting...
- Still waiting... - Sprint deadline approaching - Security still hasn't reviewed - Ship without review or miss deadline?
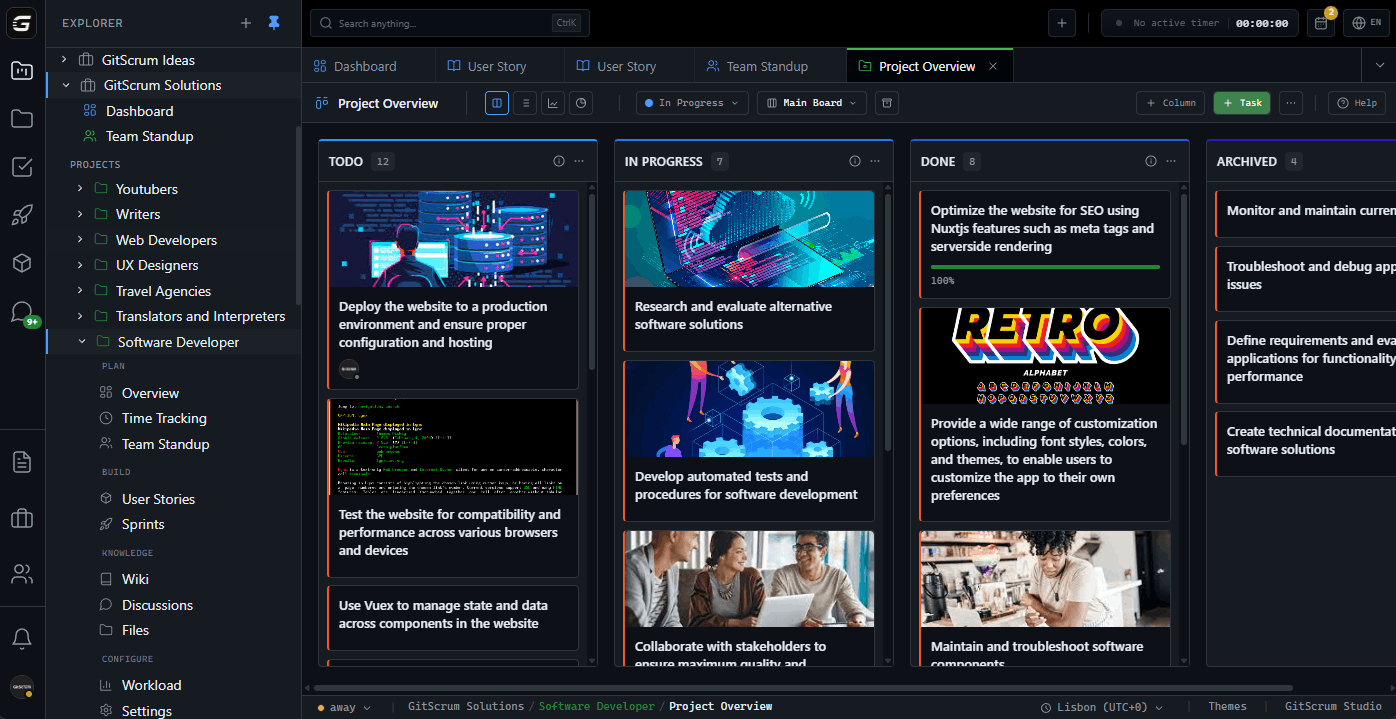
Neither option is good. GitScrum: Built for Regulated Industries GitScrum understands that some software has higher stakes: 1.
Audit Trail Everything - Who changed what, when, why - Approval chain documented - Linked to code commits - Exportable for auditors 2. Regulatory Deadline Tracking - Mark deadlines as 'regulatory' - Automatic priority escalation - Countdown visibility - No 'we forgot PCI renewal' 3.
Security Review Integration - Security review as required step - Track review status in workflow - Escalate delayed reviews - No shipping without signoff Audit-Ready Documentation When the auditor asks: GitScrum Export: Payment Processing Module Changes - Q1 2024 Change 1: Add 3D Secure authentication - Requirement: PSD2 SCA compliance - Approved by: Security Lead (Jan 5) - Code Review: Senior Dev (Jan 7) - PR 234 merged (Jan 8) - Deployed: Production (Jan 12) - Commits: abc123, def456, ghi789 Change 2: Update encryption to AES-256 - Requirement: PCI-DSS 4.0 - Approved by: Compliance Officer (Jan 15) ... Time to generate: 30 seconds Completeness: 100% Auditor satisfaction: High Regulatory Deadline Management See compliance deadlines alongside development work: Q2 Roadmap: Regulatory Deadlines: [!] PCI-DSS v4.0 migration - June 30 (52 days) [!] SOX Q2 audit prep - June 15 (37 days) Feature Work: [ ] New credit scoring model - May 30 [ ] Mobile app redesign - June 20 Stories Tagged for PCI-DSS: - Upgrade encryption libraries (IN PROGRESS) - Update key rotation (NOT STARTED) <- At risk!
- Audit logging enhancement (DONE) Know if you'll miss regulatory deadlines before it's too late. Security Review Workflow Build security review into your process: Workflow: Fintech Feature 1.
Development (branch created) 2. Code Review (PR opened) 3.
Security Review (REQUIRED) 4. QA Testing 5.
Compliance Sign-off 6. Production Deployment Security review not optional.
Can't skip to step 4. Escalation Rules: - Security review pending > 2 days: Alert security lead - Security review pending > 4 days: Alert CTO - Security review pending > 7 days: Block sprint completion No more 'we shipped without security review.' Compliance Tagging Tag stories by compliance requirement: [PCI-DSS] Update cardholder data encryption [GDPR] Implement right to deletion [SOX] Add financial reporting audit trail [PSD2] Strong customer authentication Filter by compliance area: - 'Show all PCI-DSS work in progress' - 'What's blocking GDPR compliance?' - 'Who's working on SOX requirements?' Change Impact Assessment Fintech changes need impact analysis: Story: Update payment routing logic Impact Assessment: Affected Systems: [Payment Gateway] [Fraud Detection] [Reporting] Data Touched: [PII] [Financial] [Audit Logs] Compliance Impact: [PCI-DSS] [SOX] Risk Level: HIGH Required Reviews: [Security] [Compliance] [Architecture] Don't discover impact during the audit.
Approval Chain Documentation Who approved what: Feature: New Credit Limit Algorithm Approval Chain: 1. Product Owner - Business requirement (Feb 1) 2.
Risk Manager - Risk assessment (Feb 3) 3. Compliance Officer - Regulatory review (Feb 5) 4.
Security Lead - Security assessment (Feb 8) 5. Architecture Board - Technical approval (Feb 10) 6.
CTO - Final sign-off (Feb 12) All documented. All timestamped.
All exportable. Incident Tracking Integration When things go wrong: Incident 456: Payment processing delay Severity: P1 Impact: 2,340 transactions delayed Root Cause: Story 789 deployment Related: - PR 345 (merged Feb 12) - Commits: xyz789, abc012 - Approved by: [list] - Security reviewed: Yes Post-incident: - Story 801: Fix payment routing - Story 802: Add monitoring Complete traceability from incident to code to approval.
Fintech-Specific Reports Generate compliance reports: - All changes to payment processing (date range) - Security reviews completed/pending - Compliance deadline status - Approval chain completeness - Incident-to-change mapping One click. Auditor-ready format.
GitHub Integration for Compliance Every code change linked: PR 234: Update encryption library Linked Stories: 567, 568 Compliance Tags: PCI-DSS Security Review: Approved (Feb 5) Approvers: @security-lead, @senior-dev Commits: abc123 - Update to OpenSSL 3.0 def456 - Update key generation ghi789 - Add migration script GitHub and GitScrum stay in sync. No manual documentation.
Real Scenarios Scenario 1: PCI-DSS Audit Auditor: 'Show all changes to cardholder data handling in the last 12 months.' Without GitScrum: - Search GitHub for relevant repos - Cross-reference with Jira tickets - Find approval emails - Compile into document - Hope nothing is missing - Time: 1-2 weeks With GitScrum: - Filter: Tags contain 'PCI-DSS' - Date range: Last 12 months - Export: Audit format - Time: 5 minutes - Complete: Yes Scenario 2: Regulatory Deadline Deadline: PSD2 SCA implementation by March 15 Without GitScrum: - Spreadsheet tracking - Manual status updates - Discover issues late - Panic scramble - Maybe miss deadline With GitScrum: - Regulatory deadline flagged - All related stories linked - Progress visible daily - Risks surfaced early - Deadline met Scenario 3: Security Incident Incident: Potential data exposure Regulator: 'Show us exactly what code was running, who approved it, and what's changed since.' Without GitScrum: - Reconstruct deployment history - Find all approvals - Document manually - Hope timeline is accurate - Time: Days With GitScrum: - Pull incident timeline - Show linked deployments - Export approval chain - Complete accuracy - Time: Minutes Why Fintech Teams Choose GitScrum Not Jira: - Jira compliance features require expensive add-ons - Complex configuration for audit trails - No native regulatory deadline handling Not Monday: - No code integration - No audit trail - Not built for compliance Not spreadsheets: - No automation - No code linking - Error-prone - Time-consuming GitScrum: - Audit trails included - Code integration built-in - Regulatory deadline tracking - Security review workflows - Affordable for startups Pricing - 2 users: FREE forever - 3+ users: $8.90/user/month - Audit trails included - Compliance tagging - Security workflows - Regulatory tracking 5-person fintech team: $26.70/month - Full audit capabilities - All compliance features - GitHub integration 10-person team: $71.20/month - Enterprise compliance - Advanced reporting - Multi-project tracking Compared to Jira + compliance add-ons: Thousands per year GitScrum: Everything included. The Bottom Line Fintech software requires different project management: - Audit trails for regulators - Compliance deadline tracking - Security review enforcement - Complete change documentation GitScrum delivers compliance-ready project management without enterprise prices.
Build financial software with confidence. GitScrum: Project management for regulated teams.
2 users free. $8.90/user/month.
Compliant. Auditable.
The GitScrum Advantage
One unified platform to eliminate context switching and recover productive hours.