Security-at-the-end creates a lose-lose dynamic.
If security finds issues, the team either delays (frustrating stakeholders) or accepts risk (frustrating security). The team starts to see security as adversarial rather than helpful.
Security teams get burned out blocking releases. Features get designed without security input, then redesigned when security problems are found.
The cost of late security is measured in rework, delay, and accumulated risk.
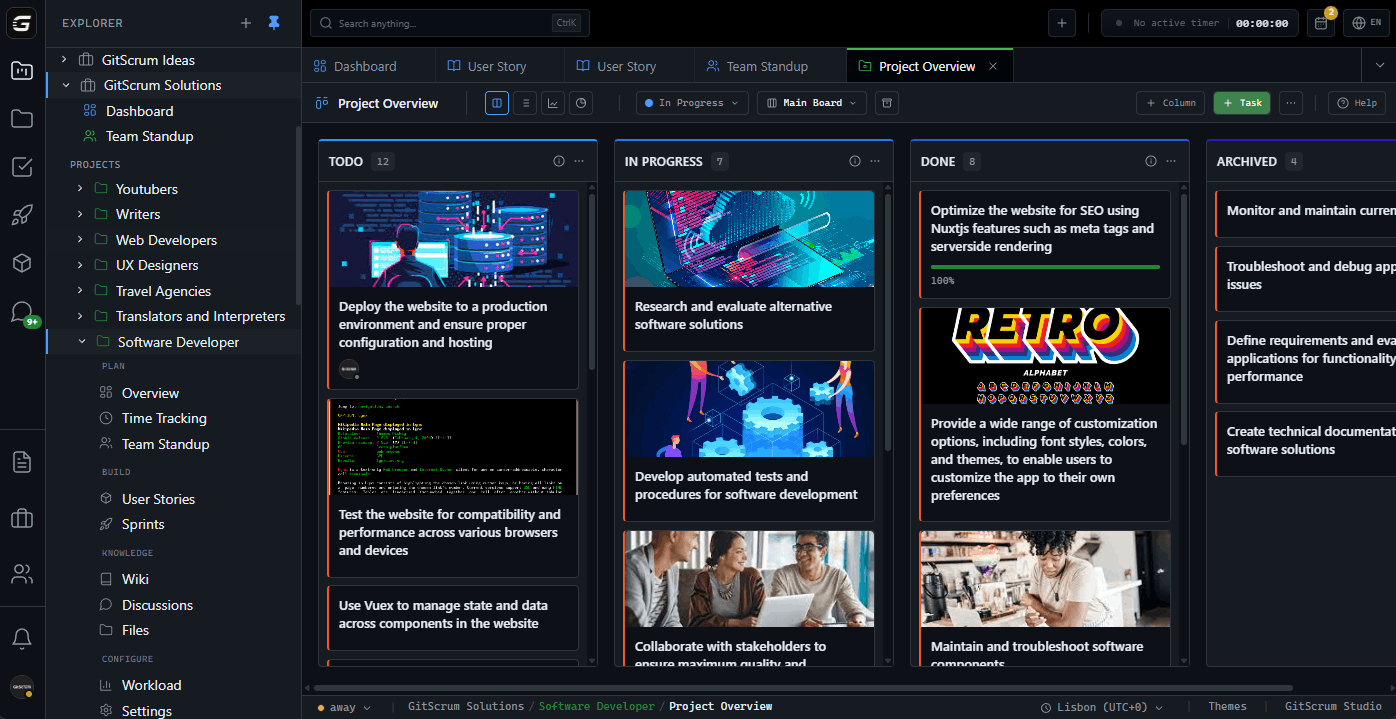
The GitScrum Advantage
One unified platform to eliminate context switching and recover productive hours.