Session timeouts exist for legitimate security reasons—abandoned sessions on shared computers create access risks.
But enterprise timeout policies often conflict directly with how developers actually work. A developer enters flow state, spends 45 minutes deeply focused on code.
During this time, they don't touch Jira, Slack, or email—they're coding. When they surface to update their task status, check a Slack message, or reference documentation, they discover every peripheral tool has logged them out.
The 30-60 minute inactivity timeouts have expired across the board. Now the developer must re-authenticate to multiple services.
Enter password, complete 2FA, wait for the tool to load their context. The interruption destroys the flow state they just achieved.
The cognitive context they held—what they were working on, why, what came next—starts to fade during the authentication friction. Multiply this across a typical day.
Deep coding session, authentication cascade. Lunch break, authentication cascade.
Meeting, authentication cascade. Each re-authentication wave represents a flow-state reset penalty.
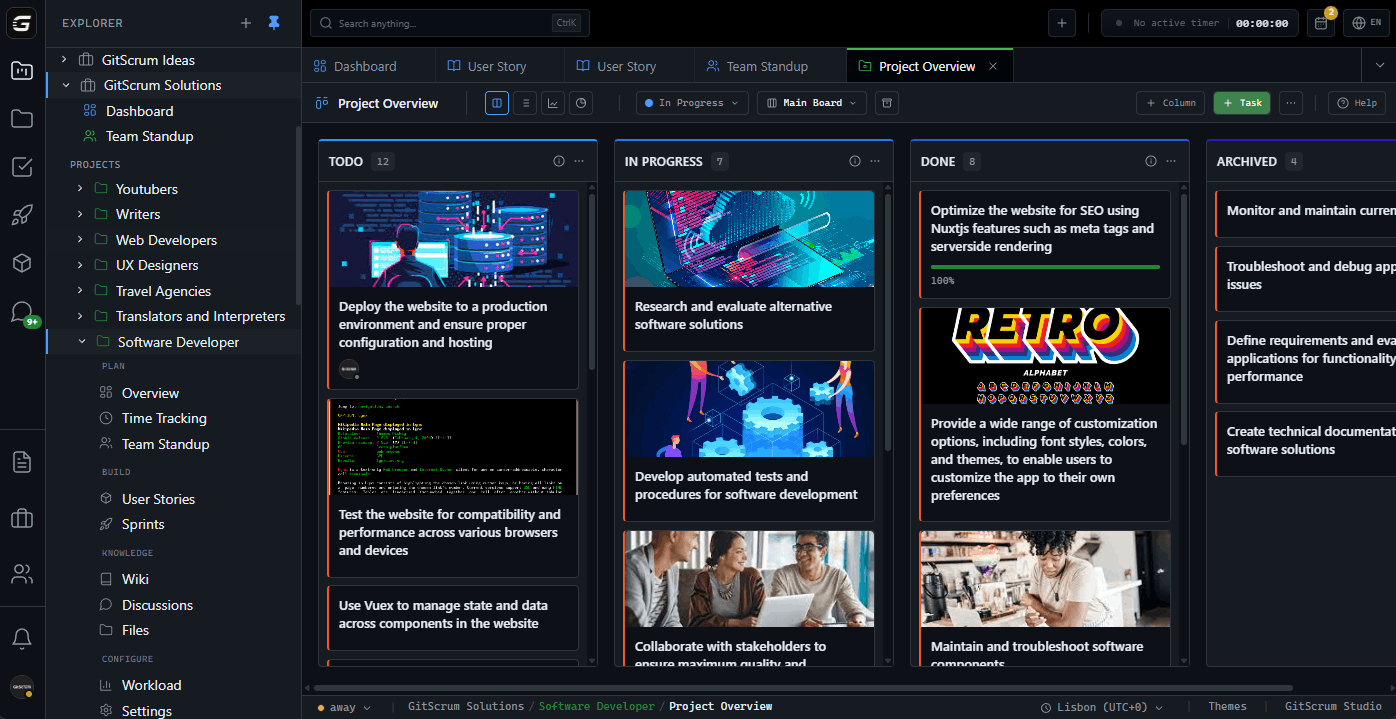
The security policies designed to protect inactive sessions are actively harming the productive sessions. GitScrum provides intelligent session management that understands deep work patterns.
Sessions remain active during legitimate work periods rather than timing out based on arbitrary inactivity windows. When re-authentication is genuinely needed, the process is streamlined.
Security serves productivity rather than competing with it.
The GitScrum Advantage
One unified platform to eliminate context switching and recover productive hours.