SSO (Single Sign-On) was designed to simplify authentication, but its implementation across multiple tools creates new failure modes.
When SSO works, developers authenticate once and access multiple services seamlessly. When it fails—and it fails regularly—the consequences cascade across the entire tool stack.
Common SSO failure scenarios include: identity provider outages that block all connected services simultaneously; token expiration that forces re-authentication during critical work; redirect loops between service and identity provider that never resolve; browser cookie issues that prevent authentication from completing; mobile app SSO that works differently than web SSO; and SSO integrations that break after tool updates. The irony is that SSO's consolidation of authentication becomes a single point of failure.
Without SSO, a Slack outage only affects Slack. With SSO, an identity provider issue can simultaneously lock developers out of Slack, Jira, GitHub, CI/CD, and cloud console.
The more tools connected to SSO, the more catastrophic failures become. Even when SSO functions, its friction accumulates.
The redirect to identity provider, authentication step, redirect back to service—each adds latency. Multiply by every tool access throughout the day and SSO adds significant cumulative delay to development work.
GitScrum provides reliable authentication with appropriate fallback mechanisms. Rather than depending on external SSO providers for every access, the platform maintains session stability and offers multiple authentication paths.
When one method has issues, alternatives exist. Authentication serves developers rather than blocking them.
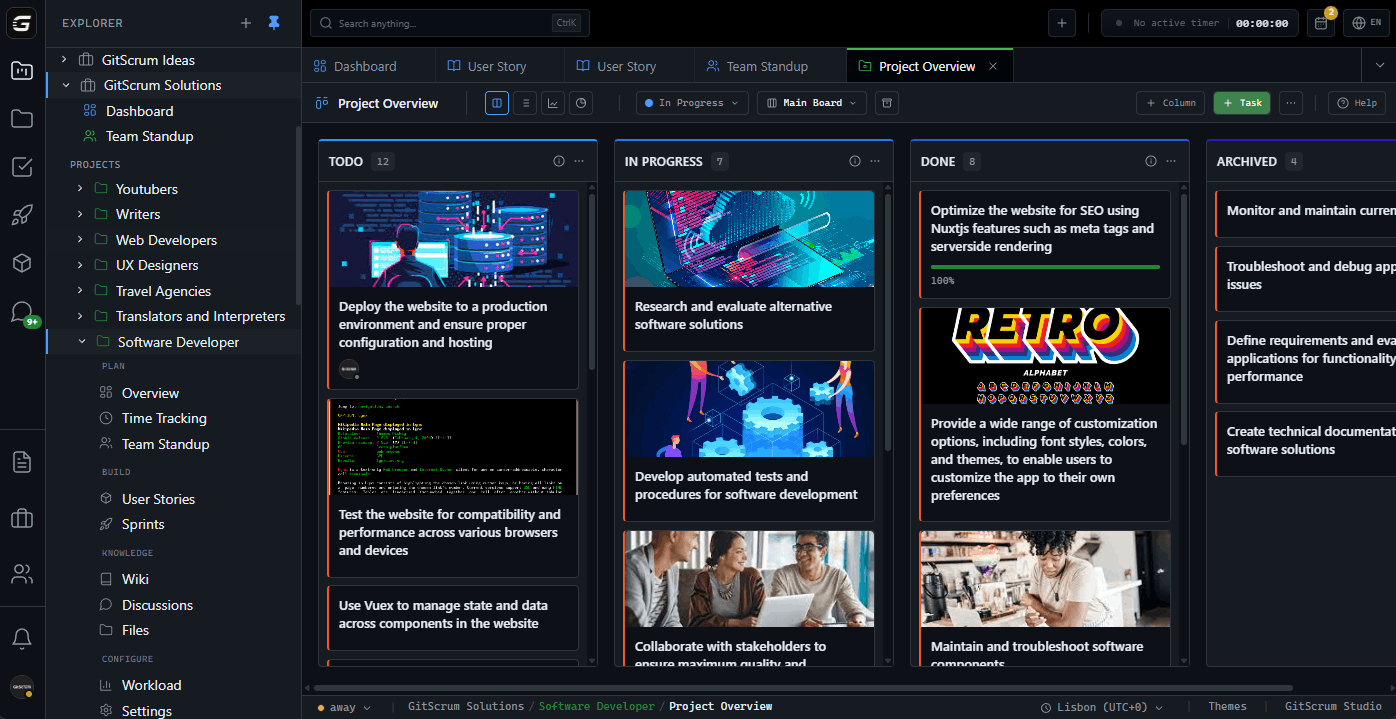
The GitScrum Advantage
One unified platform to eliminate context switching and recover productive hours.